End-to-End Encryption
Every file is encrypted on your hardware before it ever leaves your network. Only your connected devices hold the keys.
No Central Database
There is no "Gavety Cloud" to hack. Since your data lives on your physical drives at home, there is no single point of failure.
Encrypted Handshakes
Our signaling servers facilitate the connection via TLS 1.3, ensuring that even the "directions" to your server are private.
Your Privacy is Hard-Wired
Traditional data protection relies on a company promising not to look at your files. Gavety relies on mathematics.
By using Peer-to-Peer tunneling, we eliminate the middleman entirely. Your ₹1,500/year fee funds the continuous security auditing and handshake infrastructure that keeps these tunnels iron-clad.
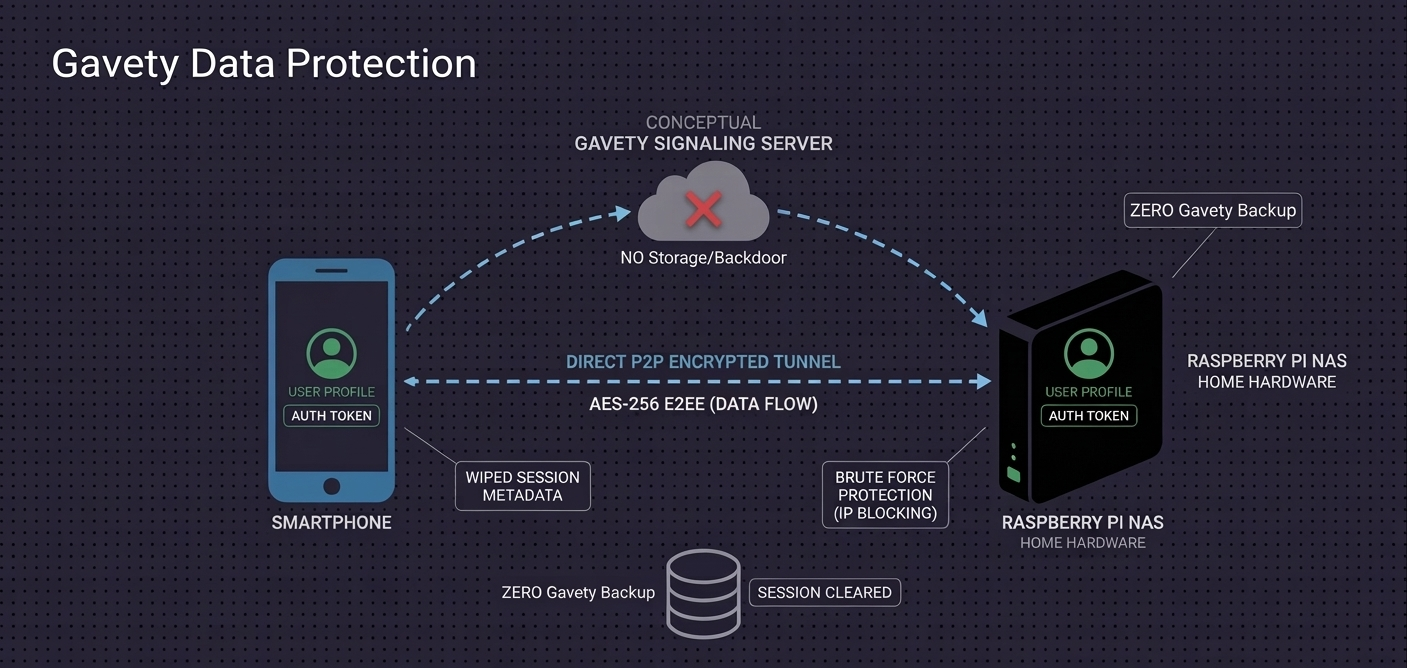
The Zero-Knowledge Stack
- E2EE (Device-to-Device): Your files are encrypted *before* they leave your phone or laptop. The decryption keys never leave your devices.
- Military-Grade AES-256: The same encryption standard used by governments to secure top-secret data.
- No Central Database: There is no large "Gavety Cloud" repository for hackers to attack. Your data is decentralized.
- Wiped Session Metadata: After a transfer, metadata is automatically wiped from our signaling servers. We "forget" you connected.
- Brute Force Protection: Automatic IP blocking prevents automated attacks on your local Raspberry Pi server.
- TLS 1.3 Handshake: All connection signals use the latest secure standard (TLS 1.3), ensuring private negotiation of P2P tunnels.